Hackers Use Smart Lock Hack for Fingerprint Theft: Researcher
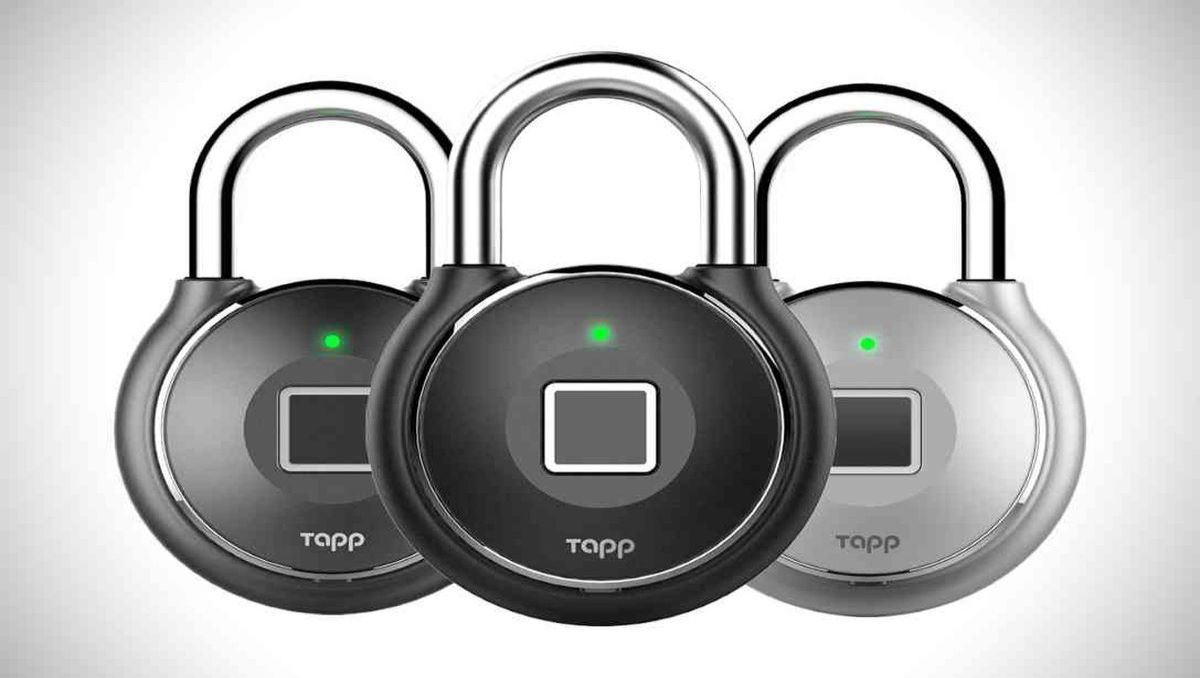
As per a recent study, consumer smart locks might be easily exploited to allow hackers to acquire the fingerprints of targeted consumers. In this regard, James Cook University Singapore published a study describing how an attacker may utilize common hardware and some hacking knowledge to stealthily gather fingerprints using a smart lock hack technique dubbed drop lock.
According to expert and senior cybersecurity instructor Steven Kerrison, the issue lies in the hardware constraints of IoT smart locks. In contrast to smartphones and tablets, which store fingerprint information and other biometric data within encrypted hardware enclaves, low-end IoT devices such as commercial smart locks lack dedicated safe storage.
Hackers Use Smart Lock Hack for Fingerprint Theft: Researcher
Kerrison stated in the report, “These devices often include less powerful CPUs and cheaper sensors, and they do not offer the same level of security as a smartphone.” Typically, this is considered acceptable based on the value of the product or what the sensor is intended to safeguard.
To demonstrate the vulnerability, Kerrison built a proof-of-concept device that could connect to a smart lock over Wi-Fi and, use either an attack or an accessible debug interface to change the lock’s software to collect and submit fingerprint data. Alternately, the lock might be taken apart and hooked directly to the controller using on-board debugging pads. In either case, it is able to provide fingerprint data that can be used against other biometric devices.
In addressing the findings with TechTarget Editorial, Kerrison remarked that any real-world attack would likely be conducted against a planned target over a predetermined length of time, as opposed to a random bulk collection of credentials.
To gather fingerprints while the lock is enabled, the attacker would need to be in close vicinity to the lock, such as the Bluetooth range. Once the print data has been acquired, it might eventually be used to get access to other devices with more stringent security measures.
While providing an explanation, Kerrison said,
The attacker needs to have a receiving device quite close to the lock — just a few meters — during the attack for the fingerprint to be transferred reliably, so that means the attack has to be more targeted than, say, leaving USB sticks lying around and waiting for people to plug them in to deliver malware into a network. That means a viable attack is more likely to be against a specific victim or group of victims, rather than random, and the assets accessible with the biometrics would have to be worth going to that amount of effort.
Check out? SRD and IoT Services Regulatory Framework Issued by PTA
PTA Taxes Portal
Find PTA Taxes on All Phones on a Single Page using the PhoneWorld PTA Taxes Portal
Explore NowFollow us on Google News!