Revenue Assurance and Fraud Management – The Life Line for Telecom Sector

Telecom is a unique business in nature, where money is earned through invisibles. One does not see voice, SMS, email or data travelling through air or cables through some device reaching at the ultimate destination at some device. The time stamping, the volumes and the numbers are recorded at various machines/systems, which eventually are translated into cash in the hands of operators in advance or arrears. But how are the operators sure that, they are getting the actual money back, against what they have sold to their customers. The reality is that nobody could ever claim having such “two plus two equal to four” mechanism in place. There always remains some differential between the earned and what should have been earned. According to Rob Mattison of GRAPA, the telcos could be losing from 1% to 30% of their potential revenues due to leakage through fraud or system malfunctioning, of which, about 1%-10% pertains to billing errors. The same numbers have been confirmed by KPMG in its survey conducted in 2009. The amount of such losses is estimated to be about $30-$40 Billion annually. The prevention of such leakage is extremely critical particularly in the markets like India, Pakistan and Bangladesh, where competition is severe, ARPUs are low and profit margins are slim.
There are following four core systems which are involved in revenue generation and collection directly or indirectly.
- Sales and Customer Relations Management System (CRM)
- Telecommunication network for service delivery
- Billing and Charging system
- Collection system
Each of the above systems has many subsystems which work with each other either in tightly or loosely integrated form under certain work flow processes. The problem is that in the rapidly growing markets the management’s main focus is always towards subscriber and network growth with lesser attention to have proper processes and procedures. This approach enhances the risk for both revenue leakage and frauds. The following diagram reflects the relationship among various system elements and processes depicting ( ) over 20 major risk areas.
Revenue Assurance and Fraud Management – The Life Line for Telecom Sector
The cause of revenue leakage can be either through System/Process misbehavior and or fraudulent activities.
One possible reason could be non-recording or incorrect placement/routing of certain events. Such occurrence could be attributed to negligence, weak processes and nonexistence of proper monitoring systems. A few examples are; incorrect charging definition on IN platform, where, international calls are routed on international routes but according to charging definitions the call is treated as local. In another case, the problem in transfer of CDRs from Mobile Switching Center (MSC), SMS Mobile Switching Center and (SMSC) and GMSC to Intelligent Network (IN used for prepaid) or to mediation system for processing postpaid and interconnect data could lead to non-billing or non-charging to the customers because of missing CDRs. Making mistakes in tariff definitions is very common, given the complexity of bouquet of services being offered by the companies under various packages with free bundles. Home Location Register (HLR) is the most critical element of the system allowing any customer to make a call who may not be registered in the billing system (in postpaid case) and incorrectly tagged in IN in prepaid case.
The companies, in the severe competition phase, generally formulate such sales and commission policies, which may increase their customer base but not necessarily add proportionate revenue which can justify customer acquisition cost. The net beneficiaries generally are the franchisees, distributors or internal sales staff. Similarly, weak credit control and collection system has proved to be another major revenue leakage source on account of sales proceeds, postpaid customers and interconnect billing. The chances of bad debt arises many folds in the absence of adequate security deposits, credit limits and an efficient credit and collection monitoring system.
The Network Fraud is related to activities related to network features, call and charging flows
Fraud is the third major source of revenue loss. The week process flows, existence of manual and non-integrated systems, flawed commission policies and week monitoring systems provide an opportunity to committing fraud, both to internal and external elements. The telecommunication sector is faced with two categories of frauds, namely network fraud and business operations fraud.
The Network Fraud is related to activities related to network features, call and charging flows. The fraud could be at a smaller scale such as making changes in customer calling rights (from local to international) and at a massive scale such as premium rate service, by pass traffic, and free or low rate charging frauds. The earlier two frauds are committed as a planned activity, where the fraudster could be a group or an individual, who enters to the network using small scale parallel system, make money and disappear. In the low rate or free of charging case, the customers at large use the system massively whenever any charging mistake by the operator is committed. Interestingly, awareness about such mistake spreads like jungle fire. The companies suffer huge losses, by the time the fact is known and problem is fixed. There are three major network related frauds currently taking place namely (1) International Revenue Share Fraud (IRSF) (2) By-pass or grey traffic fraud and (3) international roaming fraud.
The IRSF is considered to the world’s largest fraud from financial perspective both in mobile or fixed networks.
The IRSF is considered to the world’s largest fraud from financial perspective both in mobile or fixed networks. This is very organized crime, where there is chain of partners with a cascaded mode of payments between origination and destination networks. In most of the cases the latter provides both International Premium Rate Number (IPRNP) and expensive Premium Rate Service (PRS) contents. The fraudsters or partners in the traffic value chain abuse network operator’s services, not paying for traffic generated to IPRNP. The major cause of such frauds is lack of proper controls to avoid fraudulently obtained subscriptions and hacking. Very interestingly, most of such destination networks have been found in the countries, where usage of PRS is common and rates are high, like Latvia, Bulgaria from Eastern Europe, Congo, Gambia from Africa and in few cases from Western Europe.
In case of by-pass traffic, the fraudsters set up a small gateway and SIM box substation having connectivity with international carriers outside. The traffic is received and routed through the SIM box with multiple SIMs making it a local on-net call for any operator selecting cheap bundle or free minute offers. The companies lose on the deferential of high cost of international termination rate and cheap tariffs opted by the by-pass traffickers.
In case of business fraud, the sales and distribution channels, taking advantage of flawed commission policies, indulge into fake sales and in certain cases fake number portability as happened in Pakistan.
International roaming is another area, where chances of fraud are high. The operators generally avoid providing such service to prepaid customers as many of them do not have arrangements with the host networks for real time charging for prepaid. A similar risk exists in case of post-paid customers also as the time delay between calls generation and data transfer back to the home operator is a known fact and provides perfect opportunity to the fraudsters. Where the home operator can not recover the amount from its customers, it still has to pay to the host operator.
In case of business fraud, the sales and distribution channels, taking advantage of flawed commission policies, indulge into fake sales and in certain cases fake number portability as happened in Pakistan. This is very organized fraud, where the distribution channels do not remain exclusive (behind the scene) and play the game for all the operators. The new customers are maintained on one network for the mandatory period and then shifted over to other operators. The companies remain unaware of the consequences of this widespread activity for long time. In certain cases, at a limited scale the internal staff, colluding with the external sales channels makes money by tempering records and maneuvering reports. The customer service staff is generally found involved in subscription fraud, where customers are provided with the facilities; may be without proper securities or entitlement against some money. Such customers end up compiling huge bills and running away.
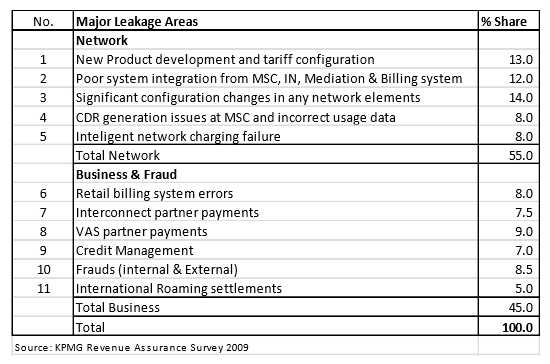
KPMG conducted an online survey in 2009 to evaluate the evolving role of Revenue Assurance and Fraud management, covering 74 operators in 46 countries. The survey results reveal that about 55% of the leakage occurs due to network related activities and processes, whereas business related activities contribute about 45% of the total loss.
To avoid the huge prospective losses, the telecom sector world over, is focusing on a having an effective and dynamic Revenue Assurance and Fraud Management (RAFM) function, which requires a very close co-ordination and support from all the other departments in addition to requisite tools, authority and empowerment from the top management.
In the network part, 39% (Sr. No. 1-3) of the leakage occur due to incorrect definitions and configurations by human and going live in the absence of an effective cross verification system. Interestingly the system malfunction contributes only 16% (Sr. No. 4-5) of the total. In the business segment 31.5% (Sr. No. 6-9) pertains to billing errors and poor credit management, whereas 13.5% revenue leakage is direct result of fraudulent activities both at domestic and international level.
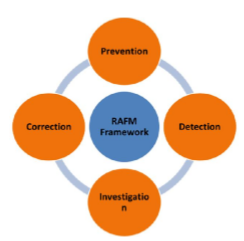
To avoid the huge prospective losses, the telecom sector world over, is focusing on a having an effective and dynamic Revenue Assurance and Fraud Management (RAFM) function, which requires a very close co-ordination and support from all the other departments in addition to requisite tools, authority and empowerment from the top management. The framework for such a system is constituted by four activities as explained below:
1. Prevention The best strategy for any operator to avoid revenue leakage is to adopt strong preventive techniques. The main features of a good preventive mechanism include implementation of well-defined processes with the engagement of all the stakeholders; integrated automated systems with electronic data flows and change management system providing relevant logs where RAFM department is able to monitor and questions certain critical activities.
The biggest threat to current telecom networks comes from non-existence of cross checking system for change management, network security control and possible malware attacks given the heavy dependence on software applications. A dynamic and well defined monitoring system in addition to hierarchal password system is the first line of defense against any fraudulent activity.
The biggest threat to current telecom networks comes from non-existence of cross checking system for change management, network security control and possible malware attacks given the heavy dependence on software applications.
2. Detection One key activity for any RAFM department is to have an early error/fraud detection mechanism. This is done through a system which can generate alarms on abnormal behavior/activity of customer usage or charging based on certain thresholds and trends in real or near real time or at a frequency as desired. It is a realty that no matter how good a preventive system is? The mistakes do happen because of circumvention of procedures to meet quick business requirements and the fraudsters are always on the lookout to meet their greed level. A good detection system can minimize the losses provided the requisite data provisioning such as Call Data Record (CDR), subscription data is ensured in an automated environment at a predefined frequency. Given the growing sense of securing against revenue stealing, the companies are investing heavily in conducting gap analysis and deploying efficient and dynamic RAFM systems developed by international solution providers.
3. Investigation Once the revenue leakage and fraud is detected; it is a mandatory requirement of any RAFM function to investigate the incidence thoroughly based on 5 Ws as described below: What ? – The nature of activity. Is it usage, charging or status related? Is it mistake or fraud? Where ? – The location of activity being local or international? Internal or external? When ? – The timing of the activity. Who ? – Who did it? Employee, franchisee or collusion? Own customer or roamer? Why? – Knowing the motive. Determining, whether the activity should be categorized as fraud or a result of mistake
The strong investigation system is always an essential supplement to preventive system. This requires proper set of tools, a group of analysts, readily available data and dedicated support from other departments. A good investigation mechanism is a must to know and fix the problem, identify the system weaknesses and devise preventive controls from future occurrence. Unlike internal audit, the investigation in RAFM is a dedicated and perpetuated activity, which is initiated immediately on occurrence of any alarm even if such alarm is proved to be false at the end. It is an interesting and proven fact that investigation of any incidence has always lead to unfolding some other unknown weaknesses and/or incidences which remain hidden given the diversity and complexity of telecom networks and systems.
4. Correction No matter, how efficient RAFM function is in prevention, detection and investigation, the stoppage of revenue leakage is largely dependent on a quick and effective correction system. It is a combination of strong and tractable follow up functionality within RAFM and action oriented dedicated resources in other departments such as customer services, IT and technical. It is however observed that more effective and efficient support from other departments is better ensured if the top management is aligned and committed to the objectives of RAFM function.
RAFM has played in saving the revenue leakage, having deployed effective tools; the telcos are expanding this activity to converge into business assurance function which now includes opportunity, cost and margin assurance
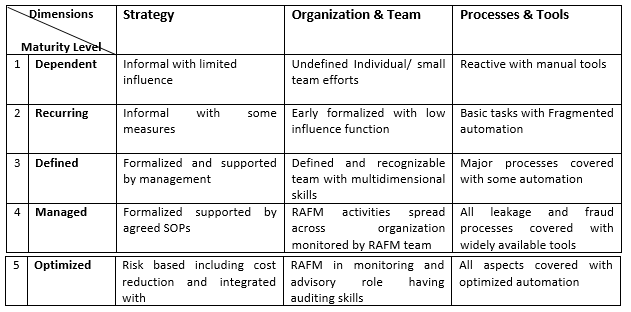
Effectiveness of RAFM function is measured by maturity assessment model as devised by TM Forum having five maturity levels (I being lowest and 5 the highest) with three dimensions.
Given the significant role, RAFM has played in saving the revenue leakage, having deployed effective tools; the telcos are expanding this activity to converge into business assurance function which now includes opportunity, cost and margin assurance. One school of thought suggests internal audit to be part of this function reporting directly to CEO or even board of directors.
The article was first published in Voice & Data by Ahmad Nadeem Syed, Head of Revenue Assurance & Fraud Management at Jazz
PTA Taxes Portal
Find PTA Taxes on All Phones on a Single Page using the PhoneWorld PTA Taxes Portal
Explore NowFollow us on Google News!